Credit card skimming (or “shimming,” in the case of chip cards) is a form of theft by which credit card information is stolen with just a small bit of technology, typically installed at the credit card terminal. Thieves install “skimmers” or devices to read and save card information undetected.
This type of theft is most common at retail outlets where credit cards are handled by employees – most frequently restaurant and bars – or where card terminals aren’t regularly monitored, such as at gas stations.
As a business owner, it is important to know what to look for to avoid risk to your consumers, headaches with the banks, and the overall pain of dealing with theft at your business.
- How Skimming Works
- Shimming – EMV Chip Cards
- How to Spot Skimmers
- Other Steps
- Chip Cards and Skimming
- Reporting Skimmers
How Skimming Works
Credit card skimmers are small, physical devices that are installed at credit card terminals. They work by copying the credit card information from the magnetic strip on the card and relaying that information to the thief via Bluetooth or stored data. Once the thief has the credit card information, they will typically sell it online, or use it to create a duplicate card. Once the duplicate card is produced, they can use that card to make purchases, without the knowledge of the cardholder. The cardholder will only be alerted once a purchase arrives on their statement that they don’t recognize.
How to Spot Skimmers
Skimmers are physical devices, meaning there are a few steps you can take to ensure your credit card terminals do not fall victim.
Inspect Your Terminal
Some credit card skimmers are molded, and now 3D printed, to fit easily into the card reader. They are made to look like part of the machine, but are often a slightly different color or quality than the machine itself. Look for anything that is protruding a little too far, slightly off center, or a different quality material than the original machine. In the image below, a skimmer protrudes past the grey sides of the panel where the reader sits.

Check For Pinhole Cameras
One way thieves attempt to grab cardholder PINs is by installing cameras around the machine. Look for little holes above or around your credit card terminal that looks like a pinhole, plug, or any other opening that seems out of place.
Wiggle the Pieces
Some more advanced skimmers are much harder to detect, since they are increasingly becoming smaller and easier to conceal. In that case, one way to do a quick check is to try wiggling various parts of your machine. If anything is looser than it should be, or not one fluid piece, that could be a sign that it has been tampered with.
Inspect the Security Seal/Tape
An obvious red flag is any change to the security seal or security tape on the pump. In the image from GoBankingRates below, an intact seal indicates a secure pump, while the voided seal is a red flag.
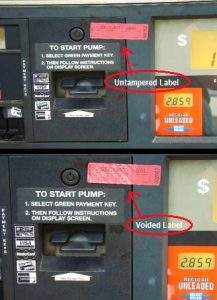
However, it’s not just voided seals that can indicate a problem. A sticker could be removed entirely and replaced with a similar sticker. Be sure you know what your stickers should look like, and that all stickers on all pumps are uniform. Any deviation could indicate a potential fraud issue.
Feel the PIN Pad
If you have a system with a PIN pad for debit card PIN entry, inspect and feel the PIN pad. Some fraudsters will install an overlay, making your PIN pad thicker or making the keys seem harder to press. The overlay is designed to grab PIN data, since the original PIN pad integrated into your system is encrypted.
Unfortunately, as credit card skimming becomes more advanced, some thieves find ways to integrate the skimming device internally, making it harder to detect the skimmer. If possible, options like applying branded security tape over the compartments or seams of the machine can help identify if the machine has been opened by an unauthorized person.
Detection Devices
Skimmer detection has been a popular idea, and a few companies have offered solutions, but nothing that has stood out as a go-to answer. In the fall of 2017, SparkX released a smartphone app called Skimmer Scanner for Android devices. The app, which was developed after determining that certain skimming devices used at gas stations in Colorado are similar to ones used nationwide, detects some skimmers via Bluetooth. Using the app can potentially help alert you to possible fraud concerns posed by skimmers. However, at the time of this update in 2023, there is not much information on whether the app is still usable and not a lot of alternatives.
Related Article: Credit Card Processing 101.
Other Steps
Beyond inspecting your physical terminal, it is always a best practice to conduct thorough background screening on employees, as skimmers are most easily installed by those who have direct access to the machine. This is particularly true of situations where employees aren’t closely monitored and can install skimmers privately.
In addition, making sure transactions are performed in front of the customer reduces the risk of claims being made against your business. If it is necessary to your business for employees to bring cards to a separate place to run credit card transactions, it is a good idea to have a manager or other employee present – not as a comment against the integrity of the employee, but more as a witness that your employees are following correct protocol in case of a skimming incident.
Chip Cards and Skimming
EMV (chip card) compliant technology was the major combatant against skimmers, as the chips made it much harder for current skimming machines to work.
However, chip cards aren’t a guarantee against skimming. As Krebs on Security reported in 2015, “shimmers” or skimmers that can specifically target chip cards, have been found in a few locations in Mexico. They’ve more recently been located in Canada and Europe as well. In 2023, Chargebacks911 posted an article on shimmers, noting that skimming attacks were 700% in 2022.
Krebs on Security notes that banks do have the ability to run a simple check to see if cards are counterfeit magstripe cards that have been encoded with stolen data, but the check isn’t foolproof.
How Shimming Works
Skimming information from an EMV chip card is known as shimming.
“Shimmers” work similarly to skimmers in that they steal information from your card. The devices themselves are different, however. As reported by Krebs on Security, shimmers are paper thin devices that sit between the chip on your card and the chip reader. It records chip data as the POS system or ATM reads it.
But, and this is important, chips include a layer of protection not available on magstripe cards. It’s a dynamic card verification value (CVV) sent to the issuing bank at the time of the transaction. The problem is that if a bank has not set up its verification process properly, the transaction may still be approved without that correct dynamic CVV.
For the most part, shimmers are not very effective tools for stealing card data just yet. A thief who retrieves chip data cannot clone a new chip card, for example. Instead, they would need to clone the data to a magnetic strip card and attempt to use that. And as long as the bank requires the correct CVV, they would not be able to use the chip data to make purchases.
Now that EMV chip cards are so common, one way you can protect your business is to take extra precautions when a customer does use a magstripe card, such as checking ID.
We’ll continue to update this section as skimming/shimming technology advances.
Related Article: EMV Chip Card Scams.
Reporting Skimmers
If you find a skimming device at your business, report it to the police and your credit card processing company. They will assist you from there. If you suspect a skimmer is being used at your business, do not continue to run credit cards through the compromised machine.
Protecting yourself against skimming schemes as a business owner means protecting your customers as well. The steps you take in safeguarding your terminal not only protect your best interest, but also keep your customers happy and coming back. Be proactive about physically inspecting your credit card machines regularly, and implementing procedures to minimize employees’ or external fraudsters’ time alone with your machines.
So the scanners only have one slot for both chip and swiping. Current chip cards still have a magnetic strip that a lot of places still accept. Is there any way to conceal this?
To conceal magnetic strips? Not really. Also, many places don’t have chip readers, so using magstripe would be the only option for those.