For many organizations, achieving and maintaining PCI compliance can be difficult and time consuming.
Some businesses aren’t sure where to start with PCI, while others struggle to sustain PCI compliance over time. If you’ve tried searching for information, you know that the articles available are often confusing, incomplete, or overly technical. Some may not even apply to your business type or industry.
So what’s the trick? Understanding what you need to do, in plain language. Here are 7 best practices to help you achieve and maintain PCI compliance. You can also use the comments section at the bottom of this post to ask questions or give information about your experience with achieving and maintaining PCI compliance.
If you’re new to PCI, start with our guide: What is PCI Compliance?
1. Perform a Risk Assessment
You can’t protect your business from unknown risks. To get started, figure out what threats your organization faces, the vulnerabilities in your environment, the likelihood that threat events will occur, and the magnitude of impact should they happen.
Use a formal risk assessment framework, such as NIST 800-30, to take a methodical approach to documenting and addressing the most important risks that face your organization. This will help you identify and rank risks, and ensure that appropriate resources are allocated to mitigate those risks.
See also: What is a Risk Assessment, and Why Does Your Business Need One?
2. Determine Your Scope
Determining scope for your organization means identifying the people, processes, and technologies that interact with or could affect the security of cardholder data. These elements are subject to PCI DSS requirements.
System components that may be in scope for your environment include:
- Networking devices
- Servers
- Applications
- Workstations
Understanding where credit card data is entering your system and where it goes from there is critical to securing that data. Create a data flow diagram for all in-scope networks. This will help you to properly understand the PCI scope of your environment by documenting where and how your card data is received, stored, and transmitted.
3. Segment Your Network
Network segmentation is done by physically or virtually separating systems that store, process, or transmit card data from those that don’t. While network segmentation isn’t required by PCI DSS 3.2, it’s a good idea if you’re looking for ways to reduce cost, time, and effort on achieving compliance. Segmenting can be done through firewalls or physical gaps.
Segmentation that meets the PCI DSS definition can be difficult, especially if you don’t have a technical security background. If you implement segmentation, engage a security professional to double check your work. Be aware that some Self-Assessment Questionnaire types require you to do penetration testing on segmentation controls every six months and after any changes.
A note on Self-Assessment Questionnaires (SAQs)
There are multiple types of SAQ and which one you’ll need to complete depends on your business. This list from SecurityMetrics details the available SAQs:
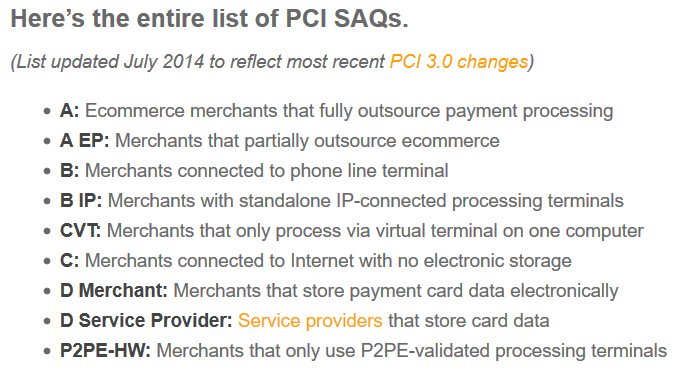
Source: http://blog.securitymetrics.com/2014/07/which-saq-is-right-for-me.html
You can also check with your processor for assistance regarding PCI compliance and completing your annual self-assessment questionnaire.
4. Run Regular Vulnerability Scans and Pen Tests
No business environment is perfect, which is why it’s important to perform regular vulnerability scans and penetration tests. By consistently checking for security holes, you can find potential issues before they become bigger problems.
Many organizations confuse vulnerability scans with pen tests, or use the names interchangeably. However, they are significantly different in how they are performed and the level of information you can receive from them.
Vulnerability scanners are tools that scan systems, networks or applications for known weaknesses. They are typically automated and designed to be non-intrusive.
Penetration tests involve both automated and manual tools. They might start with information presented in vulnerability scans, but pen tests go far beyond knowing vulnerabilities exist. In a pen test the tester attempts to exploit those vulnerabilities to gain access to your environment.
We recommend you run vulnerability scans quarterly and penetration tests annually, at a minimum. SecurityMetrics can help if you need a Vulnerability Scan.
5. Focus on Employee Training
Did you know that according to The Wall Street Journal, employees and corporate partners are responsible for 60% of data breaches? Your employees are your weakest security link, yet many businesses don’t spend enough time on security training.
Create tailored security training for individual employee roles. For example, your IT director will require more extensive training than your front desk manager. Train your employees monthly instead of yearly. Retention comes through repetition, so your employees will have better security awareness through regular reminders.
See also: Employee Training in Data Security: What You Should Do.
6. Document Everything
Documenting your policies and procedures is important since it helps employees understand what has been done and what needs to be done. Documenting the results of a formal risk assessment helps employees and decision-makers know where problems still exist in your environment. Good documentation keeps your security efforts organized and legitimate.
Documentation also simplifies the PCI process and provides a baseline for security training materials. By writing down your policies, you solidify your intentions for implementing security and training employees.
Whenever you make changes to your organization’s security, have your employees document the change. Review the documentation often (quarterly, if not monthly) to make sure it offers a clear, auditable trail to ensure accountability for changes.
7. Work with a Security Professional
Security experts and Qualified Security Assessors (QSAs) are resources that don’t get used enough. You should always consult a security professional with any update to the PCI DSS (e.g., PCI DSS 3.2).
QSAs go through intense training to understand PCI DSS and data security. They have the technical expertise to help you through the PCI process.
Related Article: Qualified Security Assessors and PCI Compliance.
If you’re a small business, you likely won’t need a PCI DSS audit, but you should still talk to a PCI professional to make sure you’re on the right path to PCI compliance. What it costs up front will save you money in the long run.