Taking credit cards is necessary these days. So is protecting your business from potential fraud those cards can bring.
Many businesses, especially smaller companies, don’t think much about credit and debit card fraud. But oversights and not using proper anti-fraud tools can add up to expensive mistakes. Taking precautions can help minimize your risk.
- Fraud Prevention for Business
- Debit and Credit Card Fraud: The Consequences
- Preventing Card Fraud
- Types of Debit and Credit Card Fraud
- Anti-Fraud Tools
- Counterfeit Fraud when Using a Debit or Credit Card
- Account Takeover/Other Fraud
Fraud Prevention for Business
Cash may still be king but its dethronement seems imminent as America, and the world, turn increasingly to electronic payments. E-payments, most often requiring the use of a debit or credit card, grew “10.1 percent by number and 8.4 percent by value” from 2016 to 2017, faster than in previous years. Indeed, “since 2016, total card payments—the sum of credit card, non-prepaid debit card, and prepaid debit card payments – increased $0.50 trillion to reach $6.48 trillion by value in 2017.” Credit card payments were $3.60 trillion, constituting 55.6 percent of the total value, with prepaid and non-prepaid debit cards making up the balance of $2.88 trillion. The Federal Reserve has published data (Fig. 1) that illustrates the trend of non-cash payments from 2000 to 2017. Increasingly, the preferred method of payment for most Americans is the debit card.
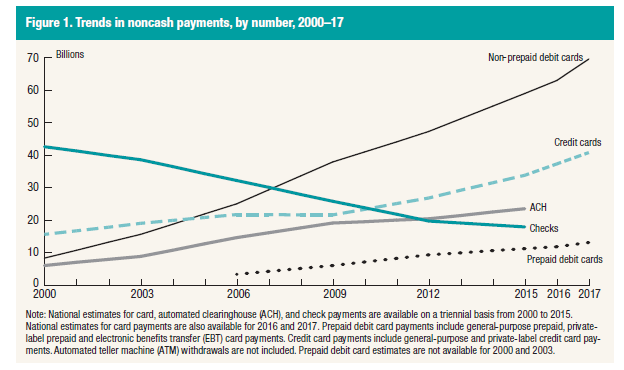
Source: Federal Reserve
A large and growing part of electronic payments are related to ecommerce, estimated by the Census Bureau at $512.6 billion in 2018, about 10% percent of total retail sales. These trends are likely to continue as more consumers take advantage of the convenience and ease of shopping online, using their debit and credit cards. Unfortunately, the increased use of debit and credit cards has increased the risk to consumers, merchants, banks and networks from fraud.
Debit and Credit Card Fraud: The Consequences
The chart below shows the extent of debit and credit card fraud in the U.S. over a recent six-year period. Most fraudulent transactions originate as card-not-present (CNP) transactions. However, counterfeit card transactions, which are transactions with fake cards using stolen information, are also substantial.
Total losses from debit and credit card fraud amounted to $5.6 billion in 2012. They had climbed by 62.5 percent to reach $9.1 billion by 2018. As alarming as this trend is, the details are more disturbing. While card counterfeit has fallen by around 15 percent in the six-year period, from $2.1-$1.8 billion, CNP fraud has risen by 146 percent, moving from $2.6 billion in 2012 to $6.4 billion by 2018. It gets worse.
Value of payment card fraud losses in the United States from 2012 to 2018, by type (in billion U.S. dollars).
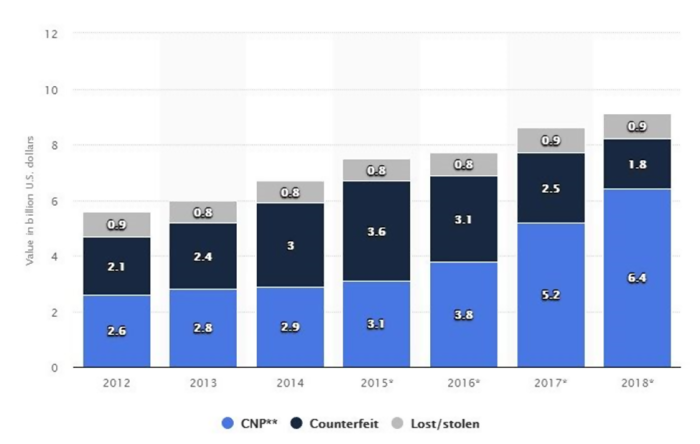
Source: Statista
As extensive as it is, the scope of card fraud extends beyond unauthorized transactions to dishonest practices such as paying card accounts with checks that bounce and fraudulent requests for a refund or return. Businesses lose revenue and merchandise from these fraudulent chargebacks, while acquirers suffer from the loss of merchant accounts and the reputational damage caused by these data breaches.
There is generally more protection for consumers. Credit cardholders receive protection from losses due to unauthorized use of the card by Regulation Z of the Truth in Lending Act. Those with debit cards have similar protection under Regulation E of the Electronic Fund Transfer Act.
Chargebacks from card-not-present transactions are first paid to the cardholder by the issuing bank, which then recovers the funds from the acquiring bank. The issuing bank is the consumer’s bank, which issues the card on behalf of one of the card networks (Visa, MasterCard, Discover, etc.) The acquiring bank is the depositary institution that maintains the business’s bank account. Fraudulent chargebacks ultimately end up as losses for the business. However, because banks typically receive chargeback requests weeks after the original payment, it may be difficult for the acquiring bank to recover from the business.
Preventing Card Fraud
Financial institutions and card issuers have adopted a comprehensive approach to security that tackles fraud on four fronts. The first step is to devalue sensitive information to make it less useful if it falls into the wrong hands. An example is tokenization, which “converts credit card numbers into randomly-generated values (tokens).”
A token is a unique number relating to a specific transaction and has no use beyond that transaction. Consequently, a cybercriminal will find the token data he has obtained to be worthless.
Second, there is increasing reliance on the analysis of data, with the object of detecting unusual patterns, for example where the location of the transaction differs from that of the cardholder’s mobile phone. Third, pushing businesses and others in the payment system to observe industry protocols, such as the Payment Card Industry (PCI) standards, for the protection of data. For example, under PCI standards, neither point-of-sale (POS) terminals nor a business’s own records, can store consumer’s credit card numbers.
Finally, alerting consumers to the dangers of card fraud and encouraging them to adopt best practices, such as monitoring their accounts regularly.
Types of Debit and Credit Card Fraud
Financial institutions and networks have categorized the trickery practiced by malefactors into four (4) broad types. These are ecommerce and remote payments fraud, which accounts for 50%; counterfeit fraud, which makes up 33%; lost and stolen cards, which comprise 9% of the total; and account takeovers and other forms of chicanery not included above, which comprise another 8%.
Anti-Fraud Tools
Techniques to combat fraud are designed to combat these four types of skullduggery.
Ecommerce and Remote Payments Fraud
Ecommerce and remote payments fraud tools include card authentication; consumer alerts; device identification; dynamic passcodes; encryption; and tokenization.
Fraudulent transactions related to online purchases or what are generally termed “card-not-present” (CNP) transactions are the most prevalent. These are transactions where neither the card nor the card holder is present, the sort that occur when someone purchases from a desktop or mobile device. The advantage for criminals is that such transactions generally will not require a PIN. A number of techniques may, however, stop them in their tracks.
Tokenization in Card Transactions
Tokenization replaces credit card numbers with randomly generated numbers that are impossible to trace back to the original data or information. A token allows you to process payment without exposing a consumer’s account number. Tokenization starts when a consumer submits their payment details – primary account number (PAN), security code, etc. – to a business. The business then requests a payment token from the network. The network shares the token information with the consumer’s bank, which allows the consumer to use the token.
Consumer Transaction Alerts
Consumer transaction alerts are a simple and powerful way to detect fraudulent activity. Sent to the cardholder’s mobile phone, email address or mobile banking app, they are an immediate indication that a transaction has been initiated. Alerts can be fashioned to reflect consumer preferences, e.g. being issued only when a transaction meets certain criteria.
Dynamic Passcode
But consumer transaction alerts are like closing the stable door after the horse has bolted. On the other hand, dynamic passcodes preempt fraud since they are required to approve a transaction. A Dynamic Passcode is a one-time unique code required to verify a transaction, sent to the card holder by mobile text or banking app.
Debit and Credit Card Authentication
Many card networks provide additional layer of analytics, intelligence, and password security to protect ecommerce transactions. For example, with Verified by Visa and Mastercard SecureCode, the issuing bank can analyze and risk-score purchases. The brands follow up with their own scrutiny, risk-scoring every transaction as it is processed and providing the intelligence to businesses and financial institutions. Potentially fraudulent transactions can then be made subject to additional security buffers. Cardholders may be asked to enter a password or be sent a text message with a dynamic one-time passcode to verify a transaction.
Encryption in Card Transactions
Encryption protects transactions by “transcribing” payment information using mathematical algorithms. Card networks follow certain best practices, such as ensuring that “cleartext” cardholder data is only available at the point of encryption and at the point of decryption. Additionally, all cardholder data and sensitive authentication data must be encrypted using only ANSI X9 or ISO approved encryption algorithms. In encryption, “cleartext” is the data before it is encrypted. The encrypted code is termed “ciphertext.”
Device Identification
Another simple way to detect and prevent fraud is by checking the unique ID of the device – desktop, laptop, or mobile phone – used in the transaction. It works on the premise that a consumer will mostly use a particular device, which, of course, is not necessarily so. In 2017, the Pew Research Center found that the typical U.S. household had five digital devices. For “typical”, Pew used the median, which means that 50 percent of U.S. households had five or more digital devices.
Device identification falls into two categories: specific and persistent. A specific identification uniquely identifies a single device and no other, while a persistent identification is one that is unlikely to change even if the device settings change. Specific IDs are generally established with cookies, while persistent IDs rely on characteristics, such as operating system name and version number, browser name and version number, and browser language, observed on the consumer’s first contact. Both types have advantages and drawbacks. Despite their specificity, cookies are easily removed for both legitimate and unsavory purposes. Persistent IDs may be more durable but lack specificity.
An aspect of device identification is its location, which can be ascertained by IP address. Here again, there are difficulties. IP addresses can change for legitimate reasons, e.g. the route data takes as it is routed through cell phone towers.
Counterfeit Fraud when Using a Debit or Credit Card
A battery of defenses – EMV technology, geolocation, tokenization and alerts – combine to stop counterfeit fraud.
EMV Technology
EMV — for Europay, Mastercard and Visa — is a global standard for cards equipped with computer chips and the technology used to authenticate chip-card transactions. An EMV chip prevents counterfeit fraud by using dynamic data; i.e. the chip generates a one-time use code that makes each transaction unique. Since the chip generates a new number for each transaction, capturing the number is pointless.
This approach is in direct contrast to the one employed by magnetic strip cards, which hold static data such as the account number, the user’s name, and the card’s expiration date.
Address Verification Service, or AVS
Address Verification Service (AVS) is one of the most widely used fraud prevention tools in card-not-present (CNP) transactions. An AVS check compares the billing address used in the transaction with the issuing bank’s address information for the cardholder. It is a common sense check, since the majority of purchases go to a customer’s address.
In many cases, you can use AVS for little or no cost.
Geolocation
Visa pioneered geolocation technology for card transactions in 2015. Essentially, it matches a cardholder’s mobile phone location with the location of a transaction. Geolocation offers one more data point when accepting or declining a transaction and may work in conjunction with other tools.
For example, the consumer may be sent a unique passcode on her mobile to confirm that she is the one initiating the transaction. Presently, Visa has combined many of its security solutions into a suite of tools called Visa 3-D Secure 2.0, which holds the promise of stronger defenses against fraud by increasing the amount and type of data used in verifying transactions.
Account Takeover/Other Fraud
Tools to detect account takeover include biometric authentication to identify identity, activity analytics that compare current online behavior with past established patterns, and card verification. Card Verification Methods (called card verification value [CVV] or card verification code [CVC] for some card brands and card identification [CID] for others) are typically required in CNP transactions, where a PIN cannot be used.
The debit or credit card carries a three- or four-digit code, which the card holder enters to complete transactions. Printed only on the card, the CVV/CVC verifies that the person making the transaction is in possession of the card.
Conclusion
Payment by debit and credit card has now become a way of life for millions all over the world, a far cry from the 10,000 consumers who signed up for the world’s first charge card, introduced by Diners Club in 1950. In the U.S. alone, card payments now run close to $7 trillion annually, according to a recent study by the Federal Reserve. But this ubiquity is beset by widespread fraud that is costing consumers, banks, and networks billions in losses.
Taking steps to protect yourself and your business means using the available anti-fraud tools. If you need help setting up your anti-fraud systems, be sure to contact your credit card processor.